Otp Generator App My Key
- Otp Generator Online
- Otp Generator App My Keyboard
- Otp Generator App My Key Location
- Otp Generator App My Key Number
Description
The OneLogin Protect OTP (one-time password) is sent through your phone to OneLogin where it is validated and then the user is logged in. If the user’s mobile device is not connected to the Internet, the user can enter the one-time password on the OneLogin App Portal. As soon as OneLogin receives a valid one-time password, the user is logged in. Oct 04, 2018 An OTP or One Time Password System is a concept to prevent spam and Unwanted hack on website and Mobile App. It helps individual users to make secured their data online on any OTP integrated. One-time password (OTP): A one-time password (OTP) is an automatically generated numeric or alphanumeric string of characters that authenticates the user for a single transaction or session. This is an RFC-2289 OTP ('One Time Password') Generator. This application generates one-time passwords in accordance with the Internet standard document 'RFC2289 One-Time Password System'.
With WP-OTP you can easily set up 2 Factor Authentication with One Time Passwords for your WordPress login.
This extra layer makes your WordPress site a lot more secure.
The new stealth mode allows for invisible OTP code entry, making your login screen look like any other, no extra OTP code input field.
Getting started
After installing and activating the plugin, every user can enable WP-OTP on their profile page.
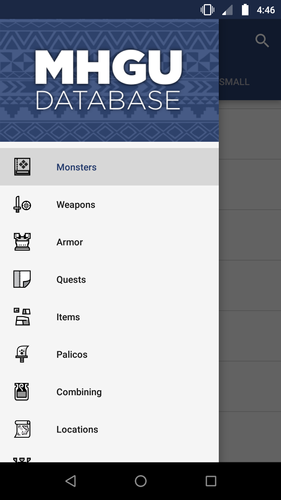
It’s as easy as scanning the provided QR Code or entering the OTP secret to any OTP generator app.
Then just activate it by entering the generated OTP and voilà , all set up.
Now, the login requires an OTP code to succeed.
Each user gets their own secret key to authenticate with, giving them control over their login security.
Development
This plugin is completely open source and a work of passion.
If you would like to be part of it and join in, make your way over to the project page now.
Also, if you have an idea you would like to see in this plugin or if you’ve found a bug, please let me know.
Configuration
WP_OTP_STEALTH: Set this totrueto enable stealth OTP mode.
Filters
There are a multitude of filters to be adjusted.
wp_otp_login_form_text: Text for input field on the login screen.wp_otp_login_form_text_sub: Subtext for the input field on the login screen.wp_otp_login_form_invalid_code_text: Error text for an invalid code input on the login screen.wp_otp_code_expiration_window: Set the window of code verification expiration.wp_otp_recovery_codes_count: Number of recovery codes to generate.wp_otp_recovery_codes_length: Length of the recovery codes.wp_otp_secret_length: Length of the secret key.
Minimum requirements
WordPress 4.6, PHP 7.1.
Donate / Support
All donations are much appreciated, thank you ðŸ™x8F
Get professional support for this plugin with a Tidelift subscription
Tidelift helps make open source sustainable for maintainers while giving companies assurances about security, maintenance, and licensing for their dependencies.
Security
To report a security vulnerability, please use the Tidelift security contact. Tidelift will coordinate the fix and disclosure.
Installation
You can either use the built in WordPress installer or install the plugin manually.
For an automated installation:
- Go to ‘Plugins -> Add New’ on your WordPress Admin page.
- Search for the ‘WP OTP’ plugin.
- Install by clicking the ‘Install Now’ button.
- Activate the plugin on the ‘Plugins’ page in your WordPress Admin.
For a manual installation:
- Upload the ‘wp-otp’ folder to the plugins directory of your WordPress installation.
- Activate the plugin on the ‘Plugins’ page in your WordPress Admin.
FAQ
No problem! When activating WP-OTP, you will also get a list of recovery codes that you can use instead of entering the OTP from your authenticator app.
Be sure to regenerate them when you run out though, or better yet, reconfigure your WP-OTP to get a new secret and a new set of recovery codes.
Yes, just click the Reconfigure button on the profile page.
Your site admin has either disabled the plugin or enabled stealth mode.
This means that you will need to add your OTP (or recovery) code at the end of your password.
Reviews
by Prakash Sharma
With the increase in cyber security threats, it has become more and more necessary to upgrade the security standards of your web applications. You need to make sure your users’ accounts are safe.
Nowadays, a lot of online web applications are asking users to add an extra layer of security for their account. They do it by enabling 2-factor authentication. There are various methods of implementing 2-factor authentication, and TOTP (the Time-based One-Time Password algorithm) authentication is one of them.
This article explains what it is, and how and why to use it. But before understanding that, let’s first briefly take a look at what two-factor authentication means.
What is Two Factor Authentication?
Two-factor authentication (or multi factor authentication) is just an extra layer of security for a user’s account. That means that, after enabling two factor authentication, the user has to go through one more step to log in successfully. For example, the usual steps for logging in to an account are:
But after enabling 2-factor authentication, the steps look something like this:
So this adds one more step to the login process. This method is more secure, because a criminal cannot access the user’s account unless they have access to both the user’s regular password and one time password.
Currently, there are two widely used methods to get that one time password:
- SMS-based: In this method, every time the user logs in, they receive a text message to their registered phone number, which contains a One Time Password.
- TOTP-based: In this method, while enabling 2-factor authentication, the user is asked to scan a QR image using a specific smartphone application.
That application then continuously generates the One Time Password for the user.
The SMS-based method does not need any explanation. It’s easy, but it has its own problems, like waiting for the SMS on every login attempt, security issues, and so on. The TOTP-based method is becoming popular because of it’s advantages over the SMS-based method. So let’s understand how the TOTP-based method works.
How the TOTP-based method works
Before understanding this, let’s first discuss what problems this method will solve for us.
By using the TOTP method, we are creating a one time password on the user side (instead of server side) through a smartphone application.
This means that users always have access to their one time password. So it prevents the server from sending a text message every time user tries to login.
Also, the generated password changes after a certain time interval, so it behaves like a one time password.
Great! Now let’s understand the workings of the TOTP-method and try to implement the above solution ourselves. Our requirement here is to create a password on the user side, and that password should keep changing.
The following could be a way to implement this solution:
This should work, but there are three main problems with it:
- How will the application generate a one time password using a secret key and counter?
- How will the counter update? How will the web server keep track of the counter?
- How will the server share the secret key with the phone’s application?
The solution to the first problem is defined in the HOTP algorithm.
Understanding HOTP:
Otp Generator Online
HOTP stands for “HMAC-Based One-Time Password”. This algorithm was published as RFC4226 by the Internet Engineering Task Force (IETF). HOTP defines an algorithm to create a one time password from a secret key and a counter.
You can use this algorithm in two steps:
- The first step is to create an HMAC hash from a secret key and counter.
2. In this code, the output would be a 20 byte long string. That long string is not suitable as a one time password. So we need a way to truncate that string. HOTP defines a way to truncate that string to our desired length.
It might look scary, but it is not. In this algorithm, we first obtain offset which is the last 4 bits of hmacHash[19]. After that, we concatenate the bytes from hmacHash[offset] to hmacHash[offset+3] and store the last 31 bits to truncatedHash. Finally, using a simple modulo operation, we obtain the one time password that’s a reasonable length.
This pretty much defines the HOTP algorithm. The RFA4226 doc explains why this is the most secure way to obtain a one time password from these two values.
Otp Generator App My Keyboard
Great! So we have found a way to obtain a one time password using a secret key and counter. But what about the second problem? How to keep track of the counter?
The solution to second problem is found in the TOTP.
Understanding TOTP:
TOTP stands for “Time-Based One-Time Password”. This was published as RFC6238 by IETF.
A TOTP uses the HOTP algorithm to obtain the one time password. The only difference is that it uses “Time” in the place of “counter,” and that gives the solution to our second problem.
That means that instead of initializing the counter and keeping track of it, we can use time as a counter in the HOTP algorithm to obtain the OTP. As a server and phone both have access to time, neither of them has to keep track of the counter.

Also, to avoid the problem of different time zones of the server and phone, we can use a Unix timestamp, which is independent of time zones.
However the Unix time is defined in seconds, so it changes every second. That means the generated password will change every second which is not good. Instead, we need to add a significant interval before changing the password. For example, the Google Authenticator App changes the code every 30 seconds.
So we have solved the problem of the counter. Now we need to address our third problem: sharing the secret key with the phone application. Here, a QR code can help us.
Using a QR code
Though we can ask the users to type the secret key into their phone application directly, we want to make secret keys quite long for security reasons. Asking the user to type in such a long string would not be a user friendly experience.
Since the majority of smartphones are equipped with a camera, we can use it and ask the user to scan a QR code to obtain the secret key from it. So all we need to do is to convert the secret key in the QR code and show it to the user.
We have solved all three problems! And now you know how TOTP works. Let’s see how to implement it in an application.
How to implement TOTP
There are some free phone applications (like Google Authenticator App, Authy, and so on) available which can generate an OTP for the user. Therefore, in most cases, creating your own phone application is not necessary.
The following pseudo codes explain a way to implement TOTP-based 2-factor authentication in a web application.
The user is asked to scan that QR code. When the phone application scans the QR code, it gets the user’s secret key. Using that secret key, the current Unix time, and the HOTP algorithm, the phone application will generate and display the password.
We ask the user to type the generated code after scanning the QR code. This is required, because we want to make sure that the user has successfully scanned the image and the phone application has successfully generated the code.
Here we use the HOTP algorithm on the server side to get the OTP-based authentication on the secret key and current unix time. If that OTP is the same as the one typed by the user, then we can enable 2-factor authentication for that user.
Now after every login operation, we need to check if this particular user has 2-factor authentication enabled. If it is enabled, then we ask for the one time password displayed in the phone application. And if that typed code is correct, only then is the user authenticated.
What happens if the user loses the code?
There are a couple of ways to help the user to recover the code. Usually when they are enabling 2-factor authentication, we can show the secret key to them along with the QR code and ask them to save that code somewhere safely.
Applications like Google Authenticator App let you generate the password by directly entering the secret key. If the user loses the code, they can enter that safely saved secret key in the phone application to generate the OTP again.
If we have the user’s phone number, we can also use the SMS-based method to send an OTP to the user to help them recover the code.
Otp Generator App My Key Location
Wrapping Up
Two factor authentication is gaining popularity. A lot of web applications are implementing it for extra security.
Otp Generator App My Key Number
Unlike the SMS-based method, the TOTP method does not require a lot of extra effort either. So this feature is worth implementing for any application.